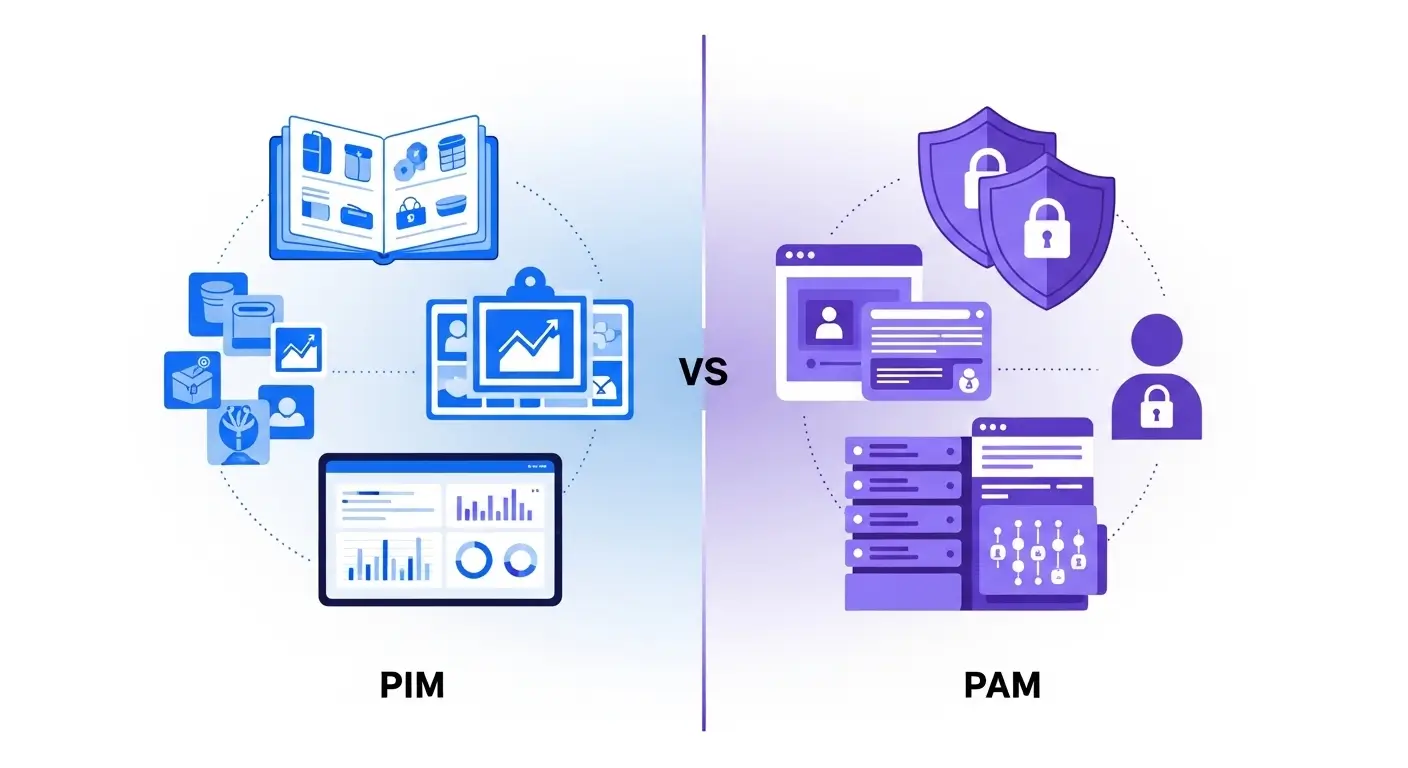
In today’s fast-paced digital business world, two acronyms PIM and PAM often cause confusion because they sound similar, yet serve completely different purposes. Understanding the difference between PIM and PAM is crucial for businesses, marketers, and IT professionals alike.
PIM (Product Information Management) is the backbone of e-commerce, helping marketers organize, manage, and distribute thousands of product details such as prices, images, and specifications across multiple online stores efficiently. It ensures customers always see accurate product information, boosting sales and improving user experience.
On the other hand, PAM (Privileged Access Management) acts as a shield for cybersecurity. IT teams use PAM to control and monitor privileged “admin” access to sensitive company data.
Key Difference Between the Two
The main difference between PIM and PAM lies in their purpose and field of application.
- PIM focuses on managing product information for marketing and sales channels.
- PAM focuses on protecting privileged accounts and controlling system access in cybersecurity.
In simple terms, PIM manages product data, while PAM manages access permissions and security.
Why Is Their Difference Important for Learners and Experts?
Understanding the difference between PIM and PAM is important for both beginners and experienced professionals.
For business teams, PIM systems ensure accurate product information across websites, e-commerce stores, and catalogs. This improves customer experience and reduces errors in product listings.
For IT and cybersecurity experts, PAM systems protect sensitive systems by controlling who can access administrative accounts. Without PAM, organizations may face data breaches, security risks, and compliance issues.
Knowing their difference helps organizations adopt the correct system for the right purpose whether improving product management or strengthening digital security.
Pronunciation
PIM
- US: /pɪm/
- UK: /pɪm/
PAM
- US: /pæm/
- UK: /pæm/
Linking Hook
Now that we understand the basic idea behind these two terms, let’s explore the difference between PIM and PAM in detail and see how they function in real-world situations.
Difference Between PIM and PAM
1. Purpose
PIM: Designed to manage and organize product information.
Examples:
- An online retailer stores product descriptions in a PIM system.
- A brand distributes product data to multiple marketplaces using PIM.
PAM: Designed to secure privileged accounts and control system access.
Examples:
- A company restricts administrator access to servers using PAM.
- IT teams monitor privileged users through PAM systems.
2. Field of Use
PIM: Used mainly in e-commerce, marketing, and product management.
Examples:
- Retail businesses manage product catalogs using PIM.
- Manufacturers maintain product specifications in PIM.
PAM: Used mainly in cybersecurity and IT infrastructure.
Examples:
- Banks protect administrative accounts using PAM.
- IT departments control server access with PAM.
3. Data Managed
PIM: Handles product-related data such as images, descriptions, and pricing.
Examples:
- Managing product attributes like color and size.
- Storing high-quality product images.
PAM: Manages credentials and access permissions.
Examples:
- Storing administrator passwords securely.
- Managing login privileges for system administrators.
4. Target Users
PIM: Used by marketing teams, product managers, and e-commerce managers.
Examples:
- Marketing teams update product descriptions.
- Product managers maintain technical specifications.
PAM: Used by IT administrators and cybersecurity teams.
Examples:
- Security teams track privileged access.
- IT staff control database administrator permissions.
5. Business Impact
PIM: Improves product consistency and sales performance.
Examples:
- Customers see accurate product details online.
- Businesses avoid listing errors across marketplaces.
PAM: Improves organizational security.
Examples:
- Prevents unauthorized access to critical systems.
- Reduces the risk of insider threats.
6. Main Function
PIM: Centralizes product information.
Examples:
- Collecting product data from suppliers.
- Distributing product details to online stores.
PAM: Controls privileged account access.
Examples:
- Monitoring administrator login activity.
- Restricting server access to authorized users.
7. Technology Focus
PIM: Focuses on product data integration.
Examples:
- Connecting product databases to e-commerce platforms.
- Synchronizing product data across channels.
PAM: Focuses on identity and access management.
Examples:
- Managing credentials securely.
- Recording privileged user sessions.
8. Risk Type
PIM: Deals with operational and data accuracy risks.
Examples:
- Incorrect product prices.
- Inconsistent product descriptions.
PAM: Deals with cybersecurity risks.
Examples:
- Unauthorized system access.
- Data breaches caused by compromised accounts.
9. Organizational Role
PIM: Supports marketing and sales operations.
Examples:
- Product launch management.
- Multi-channel product publishing.
PAM: Supports security and compliance.
Examples:
- Meeting cybersecurity regulations.
- Monitoring system administrators.
10. Core Objective
PIM: Improve product data management and customer experience.
Examples:
- Providing accurate product information online.
- Ensuring consistent brand messaging.
PAM: Protect critical systems and sensitive data.
Examples:
- Securing company databases.
- Preventing unauthorized administrative access.
Nature and Behaviour of Both
PIM:
PIM systems are organizational and marketing-focused. Their nature is to collect, manage, and distribute product information efficiently across multiple sales channels.
PAM:
PAM systems are security-focused. Their behavior centers on monitoring, controlling, and protecting privileged user accounts and sensitive system access.
Why People Are Confused About Their Use
People often confuse PIM and PAM because the acronyms look similar and are commonly used in business technology discussions. Both systems also manage important data within organizations. However, the confusion disappears once their roles are understood PIM handles product data, while PAM handles access security.
Table: Difference and Similarity
| Aspect | PIM | PAM |
| Full Form | Product Information Management | Privileged Access Management |
| Main Purpose | Manage product data | Secure privileged accounts |
| Industry | E-commerce and marketing | Cybersecurity and IT |
| Data Type | Product descriptions, images, prices | Credentials and access permissions |
| Users | Marketing and product teams | IT and security teams |
| Goal | Improve product management | Improve system security |
| Similarity | Both manage important organizational data | Both support digital business operations |
Which Is Better in What Situation?
When PIM Is Better
PIM is the better choice when a company needs to organize large amounts of product information and distribute it across multiple sales channels. Businesses with online stores, digital catalogs, or multi-marketplace listings benefit greatly from PIM because it keeps product data consistent and accurate.
When PAM Is Better
PAM is better when security is the main concern. Organizations that manage sensitive systems, databases, or infrastructure need PAM to control who can access administrative accounts. It helps prevent cyberattacks, insider threats, and unauthorized access.
Use in Metaphors and Similes
Although these are technical terms, they can appear metaphorically.
PIM metaphor examples
- “A good manager is like a PIM system, organizing every detail efficiently.”
- “Her notes were a PIM for her ideas.”
PAM metaphor examples
- “The security guard acted like PAM for the building.”
- “Strong passwords are the PAM of personal data.”
Connotative Meaning
PIM
- Connotation: Mostly neutral or positive
Examples: - “The company adopted PIM to improve product consistency.”
- “PIM made their product catalog easier to manage.”
PAM
- Connotation: Mostly positive, associated with protection
Examples: - “PAM protects sensitive systems.”
- “Security experts rely on PAM to control access.”
Idioms or Proverbs Related to the Concepts
While there are no idioms directly using these acronyms, similar ideas appear in common sayings.
“Knowledge is power.”
Example: Managing product knowledge through PIM improves business success.
“Better safe than sorry.”
Example: Companies adopt PAM to avoid security problems.
Works in Literature Mentioning the Concepts
- Product Information Management: Theory and Practice Technical/Business, various authors, 2019
- Cybersecurity and Privileged Access Management Technology guide, 2020
Movies Related to the Themes
(These topics are mainly technical, so direct films about them are rare.)
- Hackers 1995, USA (cybersecurity themes related to access control)
- The Social Network 2010, USA (technology and digital business management)
Frequently Asked Questions
1. What is the main difference between PIM and PAM?
PIM manages product information, while PAM secures privileged system access.
2. Is PIM related to cybersecurity?
No. PIM mainly deals with product data management.
3. Who uses PAM systems?
IT administrators, security professionals, and system engineers.
4. Can a company use both PIM and PAM?
Yes. Many organizations use PIM for product data and PAM for security.
5. Why are PIM and PAM important?
They improve business efficiency and system security.
How Both Are Useful for Surroundings
PIM improves the shopping experience by ensuring customers see accurate product information. PAM protects digital environments by preventing unauthorized access and reducing security risks. Together, they help businesses operate efficiently and safely in the digital world.
Final Words
PIM and PAM represent two different but essential aspects of modern organizations data management and security. Understanding their roles helps professionals choose the right solution for their needs.
Conclusion
In today’s digital environment, businesses rely heavily on technology to manage information and protect sensitive systems. The difference between PIM and PAM becomes clear when we examine their functions: PIM focuses on organizing product information, while PAM focuses on securing privileged system access.
Both systems contribute to efficient and safe digital operations, but they serve entirely different purposes. Understanding their roles helps learners, professionals, and organizations implement the right tools for their specific needs. Whether improving product data accuracy or strengthening cybersecurity, knowing when to use PIM or PAM can greatly enhance business performance and security.

Jordan L. Carter is a contributing language analyst at WordCompares.com, focusing on modern English usage, evolving vocabulary trends, and digital communication language. With over a decade of writing experience, Jordan provides insightful word comparisons that make complex language differences simple for everyday readers.